May 3, 2026
Session management ensures that when you log in to a website, your activity and authenticated status are maintained without repeatedly entering your credentials. The key to this process is secure tokens like session IDs or JSON Web Tokens (JWTs), which link authentication to your activity. Protecting these tokens and setting proper expiration policies are critical for security and regulatory compliance.
Key Takeaways:
Security strategies like token rotation, continuous access evaluation (CAE), and scoped access further enhance control. These practices not only protect sensitive data but also align with compliance requirements, ensuring safer user sessions.
Research on token expiration shows that managing token lifespans requires a delicate balance between security, usability, and meeting regulatory requirements. Security professionals and industry standards suggest specific timeframes for token expiration to minimize risks while maintaining a user-friendly experience.
Access tokens, which are essential for session management, typically have short lifespans. Research suggests a duration of 5–15 minutes for most applications. For example, Keycloak - a popular identity management platform - defaults its access token lifespan to just 5 minutes. Clifford Spielman, CEO of Duende Software, highlights the importance of this approach:
Short expiration times reduce the impact of token theft and are especially important in environments where tokens may be exposed through browser-based clients, logs, or intermediary systems.
For high-risk scenarios, such as administrative accounts, durations of 5–10 minutes are recommended. On the other hand, consumer-facing applications that prioritize ease of use often extend token lifespans to 15–60 minutes. To ensure usability despite these short durations, access tokens are typically paired with refresh tokens, which allow for seamless renewal without interrupting the user experience.
Refresh tokens are designed to provide continuity, even as access tokens expire quickly. These tokens often last between 7 and 14 days, though some use cases may extend beyond this range. Their primary role is to enable the generation of new access tokens without disrupting the user's session.
Alex Fadeev, a software engineer, emphasizes the importance of secure refresh token practices:
If your access tokens are short-lived but your refresh tokens lack rigor, your system is not actually secure. You have simply moved the risk somewhere less visible.
A common modern practice is token rotation, where each refresh action generates a new refresh token while invalidating the old one. This approach ensures that if a refresh token is intercepted and reused, the system can detect the anomaly and revoke access for the entire token family. Organizations using token rotation report noticeable reductions in unauthorized access attempts.
In addition to token-specific lifespans, many organizations enforce absolute expiration policies. These policies terminate sessions after a fixed period, regardless of user activity, aligning with NIST recommendations that moderate assurance sessions should not exceed 12 hours without re-authentication. Such measures prevent "zombie" sessions, where abandoned browser tabs remain authorized, and ensure periodic identity verification. For compliance, absolute expiration provides predictable session durations, simplifying reporting.
For sensitive or administrative operations, these limits are even stricter, often set to 5–15 minutes, ensuring that privileged access is tightly controlled. Ben from beefed.ai underscores the importance of strong token management:
Tokens are the control plane for identity and access - when the token lifecycle is weak, small faults become long-running breaches.
These findings underscore how carefully designed token expiration policies can balance security, usability, and compliance, setting the stage for further exploration into their security benefits.
Token expiration plays a key role in limiting the damage attackers can do with stolen credentials. When used effectively, it shifts session management from a passive process to an active security measure. Let’s explore how this approach reduces risks, enforces token rotation, and enables real-time access control.
Access tokens act as credentials that grant access to whoever holds them, making them prime targets for attackers. By setting short expiration times - usually between 5 and 15 minutes - organizations create a strict limit on how long a stolen token can be used. This narrow time frame significantly reduces the opportunity for exploitation.
This is especially important for stateless tokens like JWTs, which don’t allow individual revocation before they expire. Since these tokens validate themselves, expiration becomes a critical mechanism for enforcing account suspensions or role changes.
Short token lifespans become even more effective when paired with rotation strategies. Refresh token rotation ensures that each token is treated as a one-time credential. Every time a client requests a new access token, the system issues a new refresh token while invalidating the old one. If an attacker tries to reuse an outdated refresh token, the system detects the attempt and revokes the entire token family.
Ben, a contributor at Beefed.ai, highlights this advantage:
Rotation turns a stolen refresh token into a one-time credential, allowing immediate detection and revocation.
This system strikes a balance between security and usability. While short-lived access tokens reduce the risk of unauthorized access, refresh tokens maintain session continuity, sparing users from frequent re-authentication. Organizations that adopt token rotation often see measurable decreases in unauthorized access attempts.
In addition to short expiration times and rotation, Continuous Access Evaluation (CAE) provides a proactive way to address security risks. Traditional expiration relies on a token’s Time-to-Live (TTL), which means there’s a waiting period before a token becomes invalid. CAE changes this by enabling near real-time token revocation in response to security events like account deactivation, password resets, or device compromises.
With CAE, organizations can safely issue longer-lived access tokens - lasting 24 to 28 hours instead of the usual 60 to 90 minutes - because tokens can still be revoked instantly if risks arise. SecureAuth illustrates this with a real-world example:
HR triggers a termination event. Within seconds, every active session for that user - across all applications - is revoked. No waiting for token expiry, no orphaned sessions, no security gap between status change and access removal.
Advanced platforms using CAE can revoke tokens in under 4 seconds across all connected applications. This transforms token expiration from a static safeguard into a dynamic, highly responsive security tool.
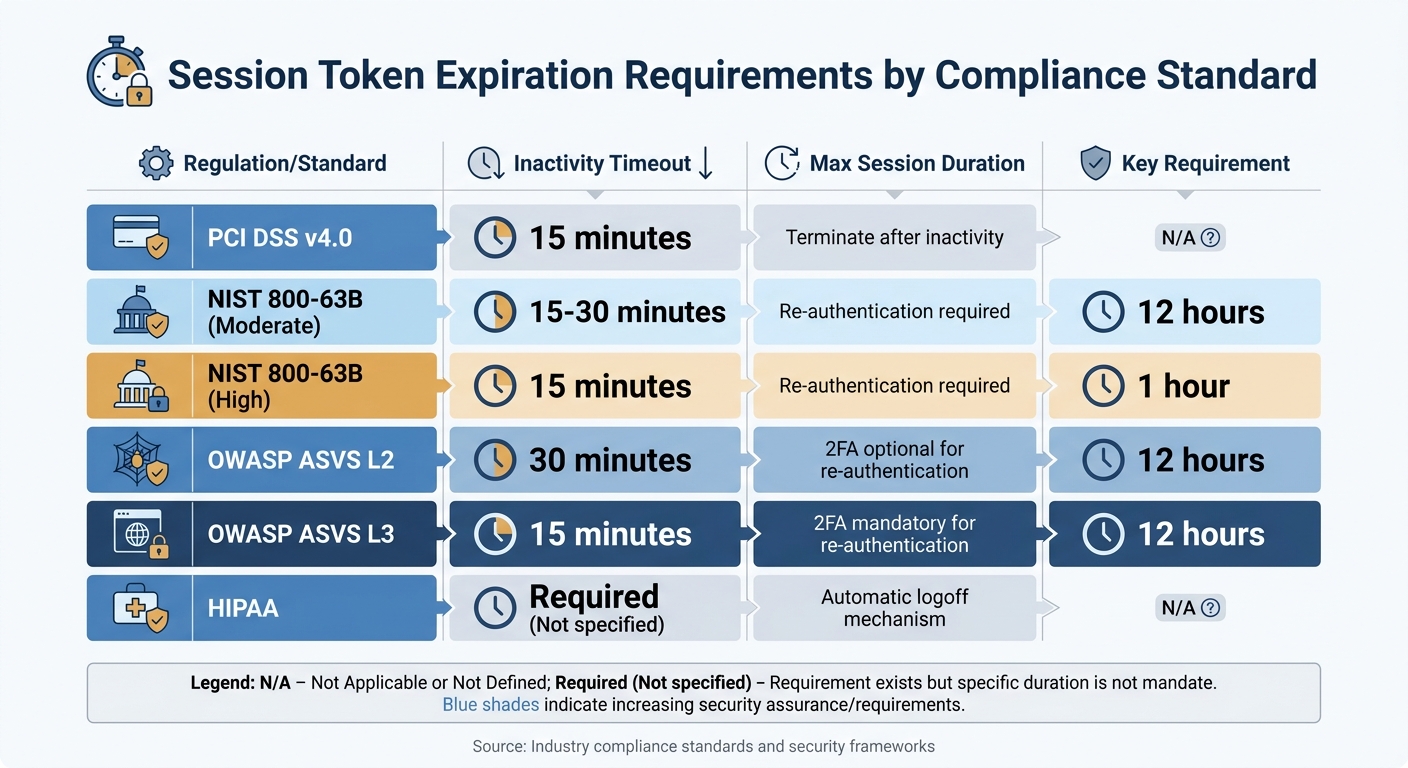
Session Token Expiration Requirements by Compliance Standard
Token expiration isn't just a best practice - it’s a regulatory necessity. Industries dealing with payment, healthcare, or financial data must implement strict session and token policies to manage session durations and ensure timely re-authentication. Below, we break down how various regulatory standards shape these requirements.
Different regulations have specific rules for managing session controls, ranging from inactivity timeouts to session duration limits.
Here’s a quick comparison of key session requirements across standards:
| Regulation/Standard | Inactivity Timeout | Max Session Duration | Key Requirement |
|---|---|---|---|
| PCI DSS v4.0 | 15 minutes | N/A | Terminate after inactivity |
| NIST 800-63B (Moderate) | 15-30 minutes | 12 hours | Re-authentication required |
| NIST 800-63B (High) | 15 minutes | 1 hour | Re-authentication required |
| OWASP ASVS L2 | 30 minutes | 12 hours | 2FA optional for re-authentication |
| OWASP ASVS L3 | 15 minutes | 12 hours | 2FA mandatory for re-authentication |
| HIPAA | Required (Not specified) | N/A | Automatic logoff mechanism |
Both mobile and web platforms impose additional security requirements to align with these regulations:
HttpOnly attribute prevents JavaScript from accessing tokens, reducing the risk of XSS attacks.Secure attribute ensures tokens are only transmitted over HTTPS connections. Ignoring these guidelines can lead to app rejection or non-compliance with broader regulations like GDPR.These platform-specific rules not only reinforce regulatory standards but also bolster token security, setting a foundation for adaptive authentication strategies.
Static timeouts alone don’t always suffice. Modern compliance frameworks emphasize risk-based reauthentication, which triggers additional verification when certain risk signals are detected - like unusual login patterns, new devices, or suspicious IP addresses.
Now that the compliance landscape is clear, let’s dive into how to apply these policies effectively. The challenge lies in balancing strong security measures with a smooth user experience, all while staying within regulatory boundaries.
Short-lived access tokens (lasting 5–15 minutes) combined with longer-lived refresh tokens (lasting 7–90 days) are a smart approach. This setup reduces the risk of replay attacks if a token is stolen, while ensuring users don’t have to log in repeatedly.
For example, Keycloak, a popular identity management tool, uses a default configuration of 5-minute access tokens, a 30-minute idle timeout, and a 10-hour maximum session. This strikes a balance by enforcing a hard limit while allowing active users to stay logged in without interruption.
Administrative sessions should expire quickly - within 5–10 minutes - and require step-up authentication for added security. On the other hand, consumer-facing applications can have slightly longer token durations, typically 15–60 minutes. Industries like finance and healthcare often lean toward shorter durations, such as 15–30 minutes, to meet stricter security needs.
"As a security best practice, we recommend that you do not set the session duration length longer than is needed to perform the role." - Amazon (AWS Documentation)
To avoid locking out legitimate users during network delays or retries, allow a small grace period of a few seconds. These carefully chosen durations provide a solid foundation for implementing additional security layers like token binding and scoped access.
Token security can be significantly improved by binding tokens to devices or cryptographic keys. Token binding ensures that a stolen token is useless unless the attacker also has access to the associated device or private key. Technologies like DPoP (Demonstrating Proof-of-Possession) and mTLS (mutual TLS) make this possible by requiring proof that the token holder possesses the private key.
Scoped access is another effective method to limit token capabilities. Instead of using a single, broad access token for multiple services, issue narrowly scoped tokens tailored to specific operations. By including scope or permissions claims in tokens, you can define precise access rights, reducing the impact of a compromised token.
For web applications, adopt the Backend-for-Frontend (BFF) pattern to keep tokens out of browser-accessible storage. This approach improves session security by managing tokens on the server side. Use secure cookies configured with HttpOnly, Secure, and SameSite attributes to further protect tokens.
Building on a foundation of secure token practices, continuous monitoring and dynamic MFA provide additional safeguards against evolving threats. Session monitoring should track user behavior, geolocation, IP reputation, and even subtle indicators like typing patterns. When anomalies such as new device logins, impossible travel scenarios, or changes in IP reputation arise, MFA should be triggered immediately.
Sensitive operations - like role changes or data exports - should require MFA, with tokens expiring in 5–15 minutes. These elevated tokens should not support silent renewal, ensuring that users must reauthenticate for high-risk actions. Additionally, monitor refresh token families closely. If a previously used refresh token is replayed, treat it as a security breach, revoke all related tokens, and require users to log in again.
Automate your response to high-risk anomalies using playbooks that revoke compromised sessions across your entire system. Tools like SIEM or SOAR can detect these anomalies and trigger appropriate actions. Authentication logs should include details like token IDs, family IDs, IP reputation, and MFA status. However, ensure sensitive information, such as raw secrets, remains protected.
To effectively align security strategies with regulatory requirements, it's important to grasp the distinct roles of different token types. Access tokens, refresh tokens, and session tokens each serve unique purposes, balancing security, scalability, and user experience. Knowing their differences helps you make informed choices for your system's needs.
Access tokens are short-lived credentials, typically lasting 5–15 minutes. They authorize API requests and verify authenticity using signature algorithms like HMAC-SHA256 or RS256. Their stateless nature makes them ideal for scalable systems, such as microservices. However, immediate revocation isn't feasible since the tokens remain valid until they naturally expire.
Refresh tokens, on the other hand, last longer - anywhere from 7 to 90 days. They allow new access tokens to be issued without interrupting user sessions. These tokens are often tracked server-side, enabling revocation when necessary. A common practice, token rotation, enhances security by generating a new refresh token with each use and invalidating the old one. As software engineer Alex Fadeev points out:
If your access tokens are short-lived but your refresh tokens are sloppy, your system is not actually secure.
Session tokens (or session IDs) operate differently. These are opaque identifiers tied to server-side session states. They offer the highest level of control, allowing immediate revocation in cases like password resets or employee terminations. However, since session tokens rely on server-side storage - commonly in databases or in-memory stores like Redis - they may pose scalability challenges compared to stateless tokens.
The table below provides a concise comparison of these token types:
| Token Type | Typical Lifetime | Security Features | Compliance Fit | Best Use Case |
|---|---|---|---|---|
| Access Token | 5–15 minutes | Signature verification (HMAC-SHA256/RS256); stateless, short-lived | High – Meets short-window requirements (PCI DSS/NIST) | API authorization, microservices |
| Refresh Token | 7–90 days | Rotation with each use, family tracking, server-side revocation | Moderate – Requires rotation and state tracking | Session continuity, mobile applications |
| Session Token | Varies (activity-based) | Server-side storage, supports immediate revocation | High – Ideal for audit trails and instant termination (SOX/GDPR) | Monolithic applications, high-security environments |
Understanding these differences ensures you can tailor your token strategy to meet both security demands and compliance standards effectively.
Managing sessions and setting proper token expiration policies play a key role in safeguarding user data and ensuring compliance with regulations. Using short-lived access tokens (lasting 5–15 minutes) alongside longer-lived refresh tokens (valid for 7–90 days) significantly reduces the risk of attackers exploiting stolen credentials.
Standards like NIST SP 800-63B and PCI DSS back these approaches. For instance, NIST recommends a session limit of 12 hours for moderate assurance and just 1 hour for high assurance levels. Meanwhile, PCI DSS requires sessions in payment environments to terminate after 15 minutes of inactivity. Beyond meeting compliance requirements, these measures strengthen technical defenses. Features like refresh token rotation and family tracking help detect token reuse attacks. Additionally, securely storing tokens in HttpOnly, Secure, and SameSite cookies - instead of local storage - protects against threats like XSS and CSRF.
Emerging tools such as Device-Bound Session Credentials and Continuous Access Evaluation push security further by enabling real-time monitoring and leveraging hardware-backed safeguards. These advancements highlight the importance of treating token policies as a core aspect of security. Organizations that prioritize these strategies are better equipped to handle both present-day threats and the challenges yet to come.
To align with PCI DSS and NIST guidelines, implement short-lived access tokens with a lifespan of 15 to 60 minutes. This approach enhances security by limiting the window of exposure if a token is compromised. To maintain user sessions without disruptions, incorporate mechanisms such as reauthentication or token refresh.
Additionally, pair these with longer-lived refresh tokens, typically valid for 7 to 14 days. Use techniques like token rotation and revocation strategies to safeguard these tokens. Together, these measures strike a balance between robust security and a seamless user experience.
When building scalable, stateless systems like microservices, JWTs (JSON Web Tokens) are a strong option. They allow token validation without needing server-side storage, making them perfect for distributed environments. However, managing them requires extra care, particularly when it comes to handling token revocation and rotation.
On the other hand, server-side session IDs are a better fit if centralized control is a priority. They make revocation straightforward and keep cookies smaller, which can be advantageous for applications with strict security or compliance requirements. The trade-off? They depend on server-side state, which can limit scalability in distributed architectures.
Using secure, HttpOnly cookies with attributes like Secure and SameSite is the best way to safeguard sensitive information. These settings significantly reduce the chances of token theft caused by XSS or CSRF attacks. Properly configuring these attributes helps ensure data protection across both browsers and mobile apps.