May 4, 2026
OAuth and OpenID Connect (OIDC) are critical for securing AI platforms. OAuth handles authorization - controlling what resources an application or agent can access. OIDC adds authentication, verifying the user's identity. Both protocols work together to ensure secure user logins, protect sensitive data, and enable AI agents to perform tasks on behalf of users.
| Protocol | Purpose | Token Type | Use Case |
|---|---|---|---|
| OAuth 2.0 | Authorization | Access Token | API access and permissions |
| OpenID Connect | Authentication | ID Token (JWT) | User logins and identity |
Why it matters: With AI agents growing rapidly, managing both human and non-human identities securely is a priority. Platforms like NanoGPT use these protocols to protect user data, limit agent permissions, and maintain trust.
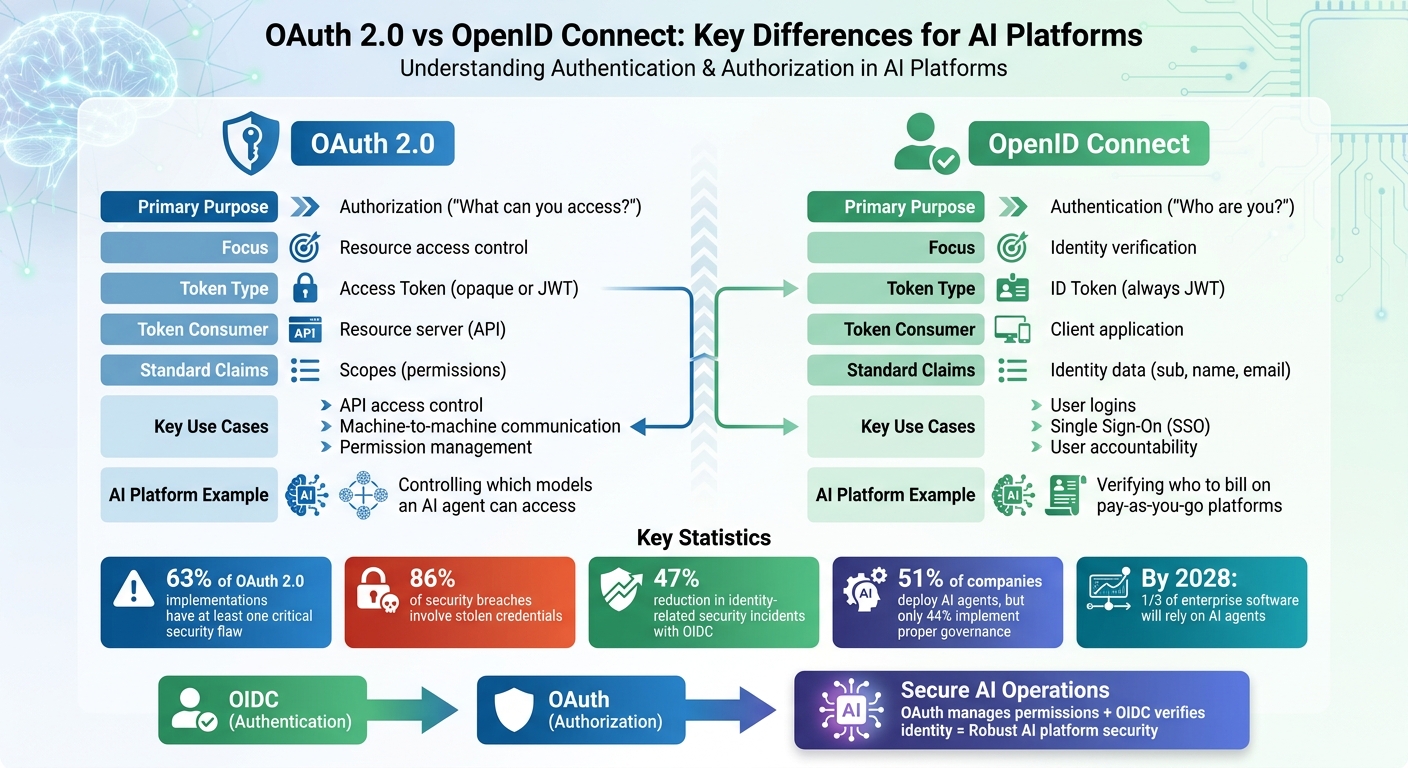
OAuth 2.0 vs OpenID Connect: Key Differences for AI Platforms
For AI platforms managing both human users and autonomous agents, keeping authorization separate from authentication is a cornerstone of secure design. Alarmingly, 63% of OAuth 2.0 implementations have at least one critical security flaw.
OAuth 2.0 addresses a key question: "What can this agent access?" It focuses solely on authorization, not authentication. For example, when an AI agent needs to interact with an API - whether to generate an image using a diffusion model or query a vector database - OAuth provides an access token. This token specifies what resources the agent can access and what actions it is allowed to perform.
OAuth employs scopes to define and limit access. Think of these as guardrails: a customer service AI agent might have access restricted to support ticket APIs but be barred from viewing financial records. This scoped token approach not only limits resource access but also ensures actions are traceable. This "least privilege" principle is crucial, especially when AI agents exhibit unpredictable behavior. As Ashur Kanoon from Aembit puts it:
"OAuth handles authorization, while OIDC handles authentication. Mix them up and you'll either over-engineer identity verification... or leave critical identity gaps".
For machine-to-machine (M2M) interactions - like an autonomous workflow accessing backend services - the client credentials flow allows systems to authenticate themselves and obtain access tokens without involving human identity verification.
While OAuth defines what resources can be accessed, a different protocol confirms who is making the request.
Unlike OAuth, OpenID Connect (OIDC) focuses on verifying identity by issuing an ID token - a signed JWT containing verified user details like name, email, and a unique identifier. OAuth grants access, but OIDC confirms identity.
This distinction becomes especially important when AI agents act on behalf of users. For instance, on pay-as-you-go platforms, OIDC ensures the platform knows who to bill before determining what resources they can use. For user logins, OIDC verifies identity and initiates a session by providing both an ID token and an access token.
A common mistake developers make is using ID tokens as API credentials. However, ID tokens are meant solely for client applications to establish identity - they should never be passed to resource servers as bearer tokens. Instead, APIs must validate access tokens by checking their signatures, expiration times, and audience claims.
Understanding the distinction between authorization and authentication is critical for AI platform architecture. Take NanoGPT as an example. Operating on a pay-as-you-go model and storing data locally, its design separates the identity layer (handled by OIDC) from the permission layer (managed by OAuth).
Here’s how it works: when a user logs in, OIDC verifies their identity and establishes a session, ensuring that every request is tied to a verified user. Later, when the user’s AI agent accesses specific models (like ChatGPT, Deepseek, Gemini, or Flux Pro), OAuth governs the permissions. The access token defines exactly which models the agent can use and what operations it can perform, while maintaining an audit trail linked to the authenticated user.
This dual-layer design is becoming even more essential as AI agents become more common. By 2028, one-third of enterprise software applications are expected to rely on AI agents. Alex Simons, Vice President of Product Management at Microsoft, emphasizes this need:
"Agents need much more granular permissions, and they need to be dynamic, easily revokable, yet auditable".
For platforms like NanoGPT, which prioritize user privacy by storing data locally, this separation ensures that even autonomous agents operate within clear boundaries, with every action tied to a verified identity and limited resource access.
OAuth and OpenID Connect rely on distinct token types and endpoints, each tailored to specific needs in securing AI platforms.
OAuth 2.0 uses access tokens to grant specific permissions for interacting with protected resources. These tokens can either be opaque strings or JSON Web Tokens (JWTs), depending on the implementation. Their primary function is to allow resource servers to validate access rights, not to share information with clients. For instance, when an AI agent accesses a dataset or model, the token scopes define what actions are allowed, such as "read:models" or "generate:images."
For machine-to-machine communication, OAuth leverages the Client Credentials Flow, enabling systems to authenticate without requiring user input. Importantly, access tokens should only be validated by the API server and never directly processed by the client.
Unlike OAuth, OpenID Connect focuses on verifying user identity rather than resource access.
OpenID Connect introduces the ID token, a JWT designed to help clients verify a user's identity. Unlike access tokens, these tokens are readable by the client application and include standardized claims like a unique user identifier ("sub"), name, and email. For example, when a user logs into an AI platform, the Authorization Code Flow with PKCE returns both an ID token (to confirm the user's identity) and an access token (to authorize API interactions).
OpenID Connect also provides additional endpoints, such as:
It’s important to note that ID tokens are strictly for identity verification and not for API authorization. For AI platforms, this means the ID token establishes a user session locally, while access tokens handle API-level permissions.
Here’s a quick breakdown of the differences between OAuth 2.0 access tokens and OpenID Connect ID tokens:
| Dimension | OAuth 2.0 Access Token | OIDC ID Token |
|---|---|---|
| Primary Purpose | Authorization (resource access) | Authentication (identity verification) |
| Format | Opaque string or JWT | Always a JWT |
| Primary Consumer | Resource server (API) | Client application |
| Standard Claims | Scopes (permissions) | Identity claims (sub, name, email) |
| Validation | API server | Client application |
| AI Platform Use | API integrations | Managing user login and SSO |
For public clients, always use PKCE and validate the nonce to guard against replay attacks. Understanding these differences ensures AI platforms can implement the right protocol for secure and efficient operations.
Let's break down how key protocols like OAuth and OpenID Connect (OIDC) are applied in AI platforms, making them more secure and efficient.
OAuth 2.0 is a game-changer for secure API interactions. Instead of using permanent credentials, it operates with temporary access tokens. For AI agents, OAuth's Client Credentials Flow ensures secure machine-to-machine communication. For instance, a customer service AI agent might be granted access to specific scopes like read:tickets or read:knowledge_base, while being restricted from sensitive endpoints. This follows the "least privilege" principle, which is critical since 86% of security breaches involve stolen credentials.
AI platforms are increasingly moving away from static Role-Based Access Control (RBAC) in favor of dynamic models like Attribute-Based Access Control (ABAC) or Policy-Based Access Control (PBAC). These approaches are better suited for the unpredictable nature of AI agents. And the shift makes sense - by 2026, over 80% of enterprises are expected to integrate generative AI APIs into their workflows. Currently, 94% of organizations already rely on OAuth 2.0 as a cornerstone of their API security strategy.
While OAuth secures API-level interactions, OpenID Connect steps in when user identity verification is required.
OpenID Connect (OIDC) focuses on verifying user identity before granting access, which is crucial when AI agents act on behalf of users. Picture an AI assistant scheduling meetings, sending emails, or accessing personal files - it needs to know exactly who it's working for. Organizations using OIDC have reported a 47% reduction in identity-related security incidents compared to older methods. Plus, OIDC supports Single Sign-On (SSO), making it easier for users to authenticate once and access multiple AI tools.
In industries like healthcare or finance, where compliance is non-negotiable, OIDC provides the assurance needed for handling sensitive data. For example, when an AI agent accesses patient records or financial details, it's vital to know who authorized the action. OIDC's ID Token includes claims like email, name, and subject identifiers, simplifying audit trails.
"The future isn't static identity. It's agentic. And we must secure it before the risks outpace our ability to manage them." - Eric Olden, CEO, Strata Identity
OIDC's offline_access scope is another standout feature. It issues refresh tokens, enabling AI agents to complete long-running tasks even when users aren't actively logged in. This aligns with predictions that by 2026, 30% of enterprises will rely on AI agents operating with minimal human oversight. Platforms like NanoGPT, which emphasize local data storage and privacy, benefit greatly from this robust authentication approach.
Deciding between OAuth and OpenID Connect (OIDC) depends on your platform's specific requirements. The choice largely hinges on whether you need authorization, authentication, or both.
OAuth 2.0 shines in authorization-only scenarios, especially in machine-to-machine communication where verifying identity isn't necessary. Instead, the focus is on controlling access to resources. For instance, if your AI services operate within a single trust boundary - like a Kubernetes cluster or a unified cloud account - OAuth is lightweight and effective. The existing infrastructure already ensures identity through cryptographic measures, making OIDC unnecessary in such cases.
A practical example? Imagine an AI agent accessing your knowledge base API to fetch data without acting on behalf of a specific user. Here, OAuth's Client Credentials Flow provides scoped and secure access without the added complexity of identity verification.
OIDC becomes critical when authentication is required. If your platform needs secure user logins, single sign-on (SSO), or ties billing to individual users, OIDC's authentication layer is indispensable. For example, if an AI agent is scheduling meetings, accessing personal files, or handling sensitive user data, you need to confirm exactly who authorized these actions.
Industries like healthcare and finance, where regulatory compliance is non-negotiable, rely on OIDC for its robust identity assurance. In fact, organizations adopting OIDC have reported a 47% reduction in identity-related security incidents compared to older methods. The ID token's standardized claims, such as email and name, simplify audit trails, making it easier to meet compliance requirements.
These scenarios often lead to combining both protocols for a comprehensive solution.
When neither protocol alone meets all your needs, combining OAuth and OIDC offers a complete solution. OIDC handles who the user is via ID tokens, while OAuth manages what resources they can access through scoped access tokens.
Consider a platform like NanoGPT, which prioritizes user privacy and offers flexible pricing. By integrating OIDC for secure user authentication and OAuth for managing API permissions, NanoGPT ensures seamless yet secure operations. For instance, users authenticate once with OIDC, while OAuth tokens control access to various AI models like ChatGPT, Dall-E, or Stable Diffusion.
"Agents need much more granular permissions, and they need to be dynamic, easily revokable, yet auditable." - Alex Simons, Vice President of Product Management, Microsoft
With 51% of companies deploying AI agents but only 44% implementing proper governance policies, selecting the right protocol - or a combination - early on can prevent future security challenges. NanoGPT demonstrates how blending OIDC and OAuth ensures secure user authentication while maintaining precise, flexible resource authorization.
OAuth 2.0 and OpenID Connect address different aspects of security in AI platforms, each playing a crucial role. OAuth focuses on authorization, determining what resources an application or AI agent can access. On the other hand, OpenID Connect deals with authentication, confirming user identity through standardized ID tokens formatted as JWTs.
This distinction has practical implications. OAuth's access tokens are designed to grant permissions to APIs and resources, making it ideal for tasks like machine-to-machine communication where verifying user identity isn't necessary. OpenID Connect takes things further by layering identity verification on top of OAuth, enabling features like Single Sign-On (SSO) and providing user claims (e.g., email, name). These features are critical when AI agents operate on behalf of users or when compliance requires user accountability.
Understanding these differences is key to selecting the right protocol for specific needs.
Choosing between OAuth and OpenID Connect - or combining them - depends on your platform's requirements. For backend tasks or system-to-system communication where identity is already established, OAuth alone works well due to its simplicity. However, for user-facing functionalities like secure logins, SSO, or billing tied to individual accounts, OpenID Connect is indispensable. Many AI platforms benefit from using both: OpenID Connect for authentication and OAuth for fine-grained resource access control.
With 51% of companies deploying AI agents but only 44% implementing strong governance policies, selecting the right protocols early can prevent security oversights. Platforms like NanoGPT demonstrate how these protocols protect user data and manage AI access effectively. Considering that 86% of security breaches involve stolen credentials, it's important to enforce measures like PKCE, token validation, and least privilege access to safeguard users and resources in today’s AI-driven environments.
OAuth can absolutely function without OpenID Connect. OAuth 2.0 is primarily an authorization framework designed to provide access tokens that allow applications to access resources on behalf of a user. However, it doesn’t address user identity verification.
On the other hand, OpenID Connect (OIDC) is an authentication layer built on top of OAuth 2.0. It extends OAuth by adding features like verifying a user's identity and issuing ID tokens. If your goal is strictly to manage authorization - granting access to resources - OAuth alone is sufficient. But for scenarios where user authentication is required, OIDC becomes essential.
ID tokens serve a specific purpose: authentication. They confirm a user's identity, essentially answering the question, "Who is this person?" However, they are not designed for authorization, which determines what resources a user is allowed to access.
APIs require access tokens, issued through OAuth 2.0, to grant permission for resource access. Attempting to use an ID token to call an API won't work because ID tokens are focused on providing user identity details for login, not the permissions needed to interact with an API.
The choice hinges on what your AI agent requires. If you're aiming for secure and scoped API access, go with an OAuth 2.1 authorization flow, such as the Authorization Code Flow with PKCE. On the other hand, if user delegation or identity verification is your priority, implement an OIDC flow that uses identity tokens. While OAuth focuses on managing resource access, OIDC builds on that by adding an identity layer, which is perfect for scenarios like compliance or tracking user actions in agent interactions.